- Email: info@clearinfosec.com
- 1800 760 5656

In an increasingly digitized world, the rapid evolution of technology has brought both convenience and complexity. As businesses and individuals embrace the benefits of connectivity, the flip side is a growing concern about cyber threats and attacks. Cybersecurity has become a paramount concern, prompting a constant search for innovative solutions to safeguard our digital landscapes. One of the most promising developments in this endeavor is the integration of Artificial Intelligence (AI) and Machine Learning (ML) into the realm of security. This blog explores how AI and ML are transforming the field of cybersecurity, revolutionizing threat detection, prevention, and response.
To comprehend the impact of AI and ML on cybersecurity, it’s crucial to grasp their core concepts. AI refers to the simulation of human intelligence processes by machines, enabling them to learn, reason, and make decisions. ML, a subset of AI, focuses on the development of algorithms that enable computers to learn patterns and make predictions based on data without explicit programming. This capability to learn from data and adapt over time forms the foundation for their application in cybersecurity.
Threat Detection and Prevention
Traditional cybersecurity solutions often rely on rule-based systems, which can struggle to keep up with evolving threats and sophisticated attack methods. AI and ML address this limitation by enabling systems to learn and adapt to new attack patterns. These technologies can analyze vast amounts of data in real-time, identifying anomalies that might indicate potential threats. They can detect even the subtlest deviations from normal behavior, reducing false positives and enhancing the accuracy of threat detection.
AI-powered systems excel at understanding and predicting human behavior, a trait invaluable in cybersecurity. By establishing a baseline of normal user behavior, these systems can identify deviations that could signify unauthorized access or compromised accounts. This behavioral analysis extends to network traffic, enabling the identification of unusual patterns that might indicate a breach.
Endpoints, such as individual devices connected to a network, are often vulnerable points of entry for cyber attackers. AI and ML contribute to endpoint security by continuously monitoring device behavior, identifying potential threats, and responding in real-time. This proactive approach minimizes the window of opportunity for attacks to propagate.
Phishing attacks and social engineering rely on manipulating human psychology. AI and ML can be trained to recognize the characteristics of phishing emails, websites, or messages, thereby reducing the chances of users falling victim to such schemes. These technologies analyze content, sender behavior, and contextual cues to determine the legitimacy of communication.
Timely response to cyber threats is critical. AI and ML automate incident response by assessing the severity of threats, classifying incidents, and initiating appropriate actions. This automation not only speeds up the response process but also reduces the risk of human error during high-pressure situations.
AI and ML-powered cybersecurity systems are not static; they evolve with the threat landscape. As attackers develop new techniques, these systems learn from emerging threats and adapt their defenses. This adaptive nature ensures that organizations stay ahead in the ongoing cat-and-mouse game with cybercriminals.
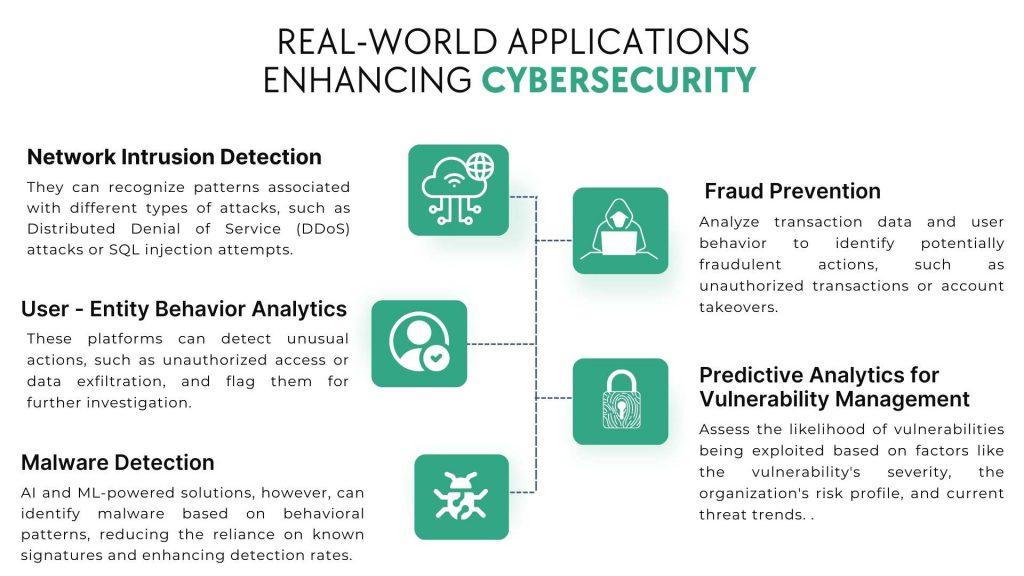
AI and ML algorithms analyze network traffic to identify suspicious behavior. They can recognize patterns associated with different types of attacks, such as Distributed Denial of Service (DDoS) attacks or SQL injection attempts. These algorithms can provide real-time alerts to administrators, enabling rapid response and mitigation.
UEBA platforms leverage AI to establish baselines of user behavior. By continuously monitoring user activities, these platforms can detect unusual actions, such as unauthorized access or data exfiltration, and flag them for further investigation.
Traditional signature-based antivirus solutions struggle to detect new strains of malware. AI and ML-powered solutions, however, can identify malware based on behavioral patterns, reducing the reliance on known signatures and enhancing detection rates.
Financial institutions employ AI and ML to combat fraudulent activities. These technologies analyze transaction data and user behavior to identify potentially fraudulent actions, such as unauthorized transactions or account takeovers.
AI-driven predictive analytics assess the likelihood of vulnerabilities being exploited based on factors like the vulnerability’s severity, the organization’s risk profile, and current threat trends. This enables security teams to prioritize patching and mitigation efforts effectively.
While the integration of AI and ML into cybersecurity holds great promise, it’s not without challenges:
The effectiveness of AI and ML depends on access to substantial amounts of data. However, ensuring data privacy and compliance with regulations like GDPR is paramount.
Hackers can manipulate AI models by providing input designed to confuse or mislead the system. This calls for the development of robust models that are resistant to such adversarial attacks.
AI models can inadvertently perpetuate biases present in training data. Ensuring fairness and unbiased decision-making is crucial, especially in security-related contexts.
AI and ML models can be computationally intensive, requiring significant processing power and memory. Organizations need to balance performance requirements with available resources.
The fusion of AI and ML with cybersecurity represents a paradigm shift in the fight against cyber threats. As these technologies continue to evolve, we can expect:
In conclusion, the integration of AI and ML into cybersecurity is a game-changer. As cyber threats become more complex, the adaptability, speed, and accuracy offered by these technologies are invaluable. However, it’s crucial to approach their implementation thoughtfully, addressing challenges related to data privacy, bias, and security. With AI and ML as allies, the battle against cyber threats takes on a new dimension, offering the promise of a safer and more secure digital future.
Copyright © 2024 Clear Infosec. All Rights Reserved.