- Email: info@clearinfosec.com
- 1800 760 5656

We know that data is what drives the technology today. Data is a distinctive type of information that is collected and translated for a specific purpose. If the data is not formatted in the right way, it does not provide any value to both humans and computers. Data is considered sensitive when it gives classified information and requires the users to have the right permissions to access it. In other words, any data that should be prevented from unauthorized access can be considered sensitive.
In order to efficiently manage data, they are organized into relevant categories according to usage. Data are categorized into groups of similar kinds. The process of organizing categorized data according to its sensitivity level is Classification and it helps to define a protection scheme for each type. When it comes to risk management and compliance, Data classification is of high importance. Data classification is a useful tactic that facilitates proper security responses based on the data being transmitted, retrieved, or updated.
Over the years, cyber-attacks are getting highly evolved, and reports say that it takes organizations an average of around 190 days to identify a data breach. If an organization is not careful enough to protect its sensitive data, they are at the risk of getting exposed to bad actors or those who are not authorized to view those data. There exist many security procedures to keep your data secured. The strategy organizations adopt to keep the data secured from reaching the wrong hands is often referred to as Data Loss Prevention or DLP.
In other words, it is a set of practices or a strategy that detects potential data breaches and ensures no sensitive data is shared, misused, or accessed by unauthorized users. It is identical with the term Data Leakage prevention and these terms are often used interchangeably. But the most commonly used term is Data Loss Prevention itself.
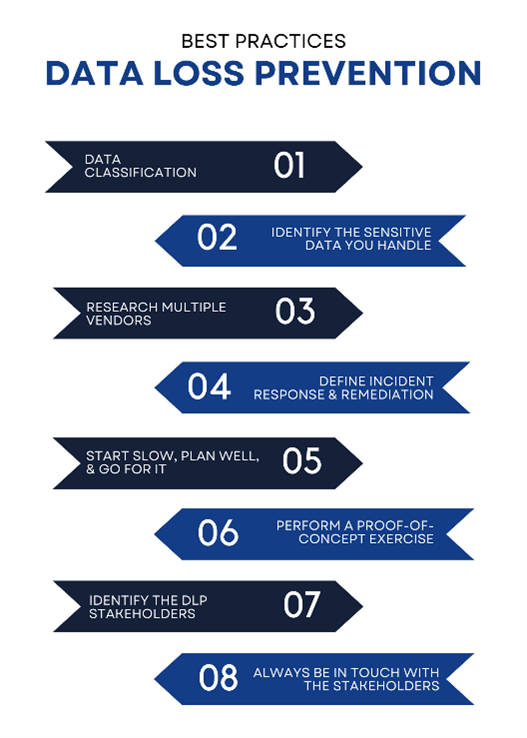
1. Data Classification
You need to be clearly aware of the data types you handle. Data classification is the process of classifying data you have under its relevant category. Some of the commonly known data types are Personally Identifiable Information (PII), Protected Health Information (PHI), Payment Card Information (PCI), and any other information that you are legally obliged to safeguard.
2. Identify the Sensitive data you handle
You should have a clear understanding of the kind of Data your organization is handling. Don’t matter you are running only a small business or even an Enterprise, this understanding is the primary level of maturity to adopt a DLP strategy.
If you are handling any Intellectual Property or Personally Identifiable Information or any such sensitive data that requires high security, it is highly recommended to adopt a DLP strategy. In order to enhance the value and creativity of your DLP program, you should engage with your Executive and Senior Leadership.
3. Research Multiple Vendors
With senior leadership, you can define your expectations for the DLP program in your organization. Consult with industry peers and vendors to learn about the DLP programs they’ve implemented, their workflow, and their level of confidence.
4. Define Incident Response and Remediation
If you are representing an Enterprise level organization, you should not buy any random DLP tool. You should take time to research and implement a complete DLP strategy. What many organizations fail to do is to plan incident management. They won’t go through the strategy process well and purchase any of the tools and fail to define a DLP incident management plan.
Make sure you have an Incident Response Team in place.
5. Start Slow, plan well and go for it
Instead of implementing every single policy checkbox while implementing a tool, go through them all and go for small wins. Start with the prior ones and implement more security on the go.
6. Perform a Proof-of-Concept exercise
The goal of this step is to duplicate the functionality and test feature sets. Upon selecting a tool, ensure that it meets your compliance needs and study carefully the deficiencies in your Incident Management program.
7. Identify the DLP stakeholders
Many researchers say that not every organization having a DLP strategy is utilizing the program efficiently. Make sure you won’t be one such. Form an internal DLP team comprised of Senior Leaders, Managers, Legal Representatives., and skilled InfoSec professionals.
If you feel hard to go through any of the DLP strategy implementing steps, try partnering with a reputed and experienced Managed Service Provider with skilled InfoSec professionals.
8. Always be in touch with the Stakeholders
Ensure you keep the stakeholders updated about the program. Never let a communication gap takes place between the DLP team and the Stakeholders. Monthly or Quarterly meetings can keep your strategy in a loop that will add value to your entire program.
With a DLP solution, you get better visibility of the data in your organization. With the right DLP solution, you get to:
1. Monitor data in motion
2. Monitor data at rest
3. Monitor how the data is being used
4. Take actions such as Delete, Log, Archive, and Quarantine
We understand that not all organizations get much investment to get a paid tool for DLP. If you are one of them, we got some solutions for you too.
1. MyDLP –
It is one of the first free software projects for data loss prevention. The project was acquired by Comodo Group in 2014 and started marketing the Enterprise version once they removed the free version from the website.
The centralized management options and Google-like search engine makes the application very easy to use. A free trial of 30 days is available for MyDLP.
2. OpenDLP
It is an open-source Data Loss Prevention tool. It is a web-based application with Data management and tracking features. It is an always-free software. You can find the application source code here.
Make sure your capital investment is put to good use and it is made after a cost-benefit analysis, risk assessment, and Vendor analysis. Understand your business model in the first place to start defining a DLP strategy. A well-planned DLP strategy and Deployment makes a DLP program successful.
Copyright © 2025 Clear Infosec. All Rights Reserved.